I was just switching branches at work and the question occurred to me: Should my book be under version control? I have gogs setup inside my VM cluster. I could map a mount point across the host/guest boundary. I haven’t needed it, yet, but that’s the sort of thing one wants setup before one needsContinue reading “Version Control?”
Category Archives: Tech
Fans Spooling Up!
It’s about time I use this computer. I have Stable Diffusion (a fairly old version) generating images from this prompt: two muscular men in jeans and tight white t-shirt full body hiking boots visible standing close outside dry hills background with a wolf sitting beside them The results are “interesting”. The faces in all ofContinue reading “Fans Spooling Up!”
We’re Doomed
I read an interesting article about AI hacking: When AI Starts Picking the Locks. There’s a lot of good stuff in there. The most terrifying sentence: And insist that human judgment — discernment, wisdom, moral responsibility — remains central to decisions about risk It’s unfortunate that almost every filter we have between birth and theContinue reading “We’re Doomed”
“Should” is Evil
That’s a fairly obvious point, but for today’s installment we have a new level of “should” stupidity. Delete should mean delete. I do not disagree. However, having the vapors when delete does not mean delete is more than a bit overwrought, especially for someone who “has been recognized by Forbes as one of America’s topContinue reading ““Should” is Evil”
I Can Has Chair!
The VESA adaptor arrived. After a moment of panic from the box (“49-inch monitors have two different mounts; be sure you have ours”), it turned out fine. The chair (it’s also the desk) is a little on the YUGE side for the room, but it does fit. I’m typing this in the reclined position, whichContinue reading “I Can Has Chair!”
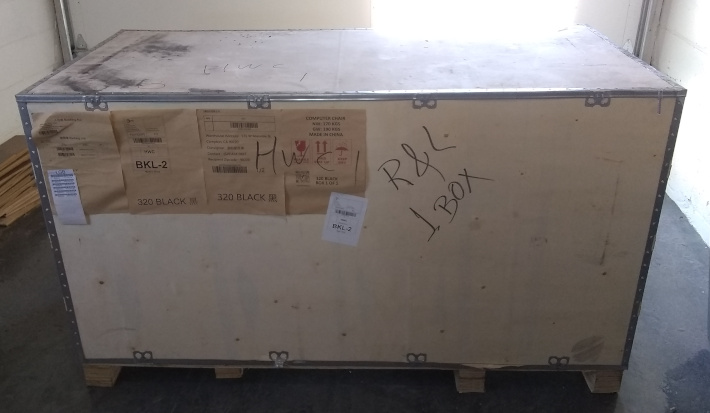
Putting a Chair Together
The new chair arrived on Tuesday. It showed up about 10:00. I abandoned work (as opposed to taking time off) to put it together. I have never seen such packing. It was seriously impressive. There must have been a company-wide Tetris contest – in hell-mode where all the pieces are curved. Whoever won decided howContinue reading “Putting a Chair Together”
My Favorite Weapon
At the very least, it’s the weapon of mine that gets the most use. It’s also cheap – at least for a weapon. No, I don’t have the laser sight. I also don’t have an annoying fly around my desk. Now, back to work…
How to Rationalize Anything
Or “How I bought an insane thing and want to feel justified about it.” I would hope that anyone old enough to drink has at least heard the phrase, “humans are not rational, they rationalize.” We do things because we want to. We come up with the logical reasons, afterward. Not always, of course (notContinue reading “How to Rationalize Anything”
Bye Bye Oculus
I bought some headphones for it, hoping for better audio. No such luck. Bad audio and blurry, pixelated graphics. It’s gone, even leaving aside that every other menu is designed to make you buy something, not be useful. Not that I used it much, but now I will use it never. Anyone want one?
1,984 Miles Across the Room
The Laird asked about getting my baking pictures out of my phone. They travel 1,984 miles (3,192 km) to get across the room. The easiest way to transfer the files from my phone to my computer is via Google Drive (it’s not as if Microsoft is a better company). Starlink satellites orbit at about 342Continue reading “1,984 Miles Across the Room”